Questionnaire Response Automation: A Solution to Security Reviews
Is your team facing an ever growing flood of risk assessments? Questionnaire response automation may be the solution.
With accelerated digital transformation and a shift in flexible work arrangements, companies are using more third party vendors to succeed. But with outsourced supply chains come increased security demands from organizations performing third party risk assessments.
As a vendor to other organizations, you probably find yourself answering the same sets of questions every week, which can go anywhere from 40 to 400 inquires. Every new relationship with a prospective customer means showing your security posture to build trust, all while the organization on the other end compiles its due diligence reporting, which can take weeks, if not months.
How much time does your team spend responding to one-off security questionnaires? How many times were you asked for a SIG Lite or a pentest this year? When was the last time a Salesperson sent the wrong document to a customer to ‘speed things up’?
There’s got to be a better way…
Like with most business process problems, technology can help. Automation and centralization are the key to solve the most common issues for vendors doing security reviews.
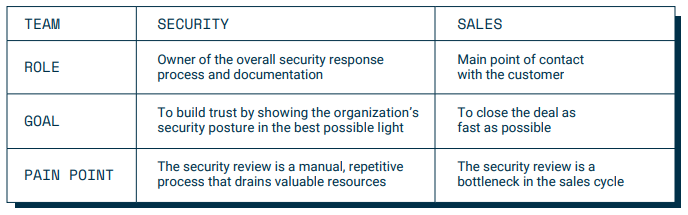
The problems vendors face often include:
- Lack of control over security documentation — Teams often face an ownership challenge: Where should the security documents sit? Who should be tasked with updating them and/or personalizing them for a particular deal?
- Time consuming and repetitive processes — The one-off nature of the manual approach makes it impossible to scale, as there’s a limit in the amount of emails and spreadsheets the same people can answer on a weekly basis. Plus, valuable hours are taken away from more strategic IT Security projects.
- Difficulty in establishing reputation — The least professional and/or slowest companies to respond will always be second-tier. Few businesses can afford losing a deal due to failing a security review. Far fewer can succeed if their reputation is bruised from always being second in line for potential deals.
Questionnaire Response Automation: Answer Once, Share Many
Beacon by ThirdPartyTrust is our questionnaire response automation tool for vendors. It allows you to build a single security profile, which works as a centralized repository for all the questionnaires, certifications, and attestations you’re usually requested, such as:
- SIG Core and Lite, Cloud Security Alliance CAIQ, and other questionnaires
- SOC reports, ISO certifications, HiTrust and many others
- Penetration tests, application scans and other attestations
- Insurance documentation and other audits

The ownership issue is fixed with user management, allowing sales teams to share and IT to maintain and edit your security profile.
Thanks to our built-in data provider integrations, you can complement this Beacon profile with objective security ratings to showcase your strength, which are provided by BitSight, RiskRecon, Osano, and other partners.
Once you profile is set up, which literally takes minutes, the magic begins. You simply invite your customers to connect in the ThirdPartyTrust platform, by sending a templated email, and they’ll be able to review your profile. With a self-service approach, they’ll find their way to your security documents and find most of their questions answered.
This allows you to be proactive in sharing your security posture and establishing reputation. More importantly, it enables a scalable process to reduce the time your team spends on security assessments.
The next time a customer requests you to fulfil security requirements, you don’t have to start from scratch. You can just build your profile once, keep it updated, and invite customers to your Beacon profile sharing only the parts of it you want them to see, through our selective sharing feature.
Watch how Beacon by ThirdPartyTrust can help you increase questionnaire response efficiency by up to 95% and reduce your overall sales cycle by up to 85%:
No matter how many new customers or periodic reassessments you need to complete, you’d be able to fulfil unlimited security reviews with the same resources.
On the other hand, enterprises struggling with follow ups and chasing dozens of vendors will find third party risk assessments a breeze.
Beacon by ThirdPartyTrust: The Easy Way of Answering Security Reviews
With Beacon, your company can take command of requests through a single security profile, including all questionnaires, certifications and attestations. When a customer asks for a certain document, you can just invite them to the ThirdPartyTrust platform to see your profile, where they’ll be able to access every piece of information in a simplified and secure manner.
These are the main benefits of using Beacon:
Maintaining Ownership Control
Instead of having sales and support staff share your company’s security documents insecurely, put a formal process in place. You will differentiate from your competition proving to your customers their data will be safe.
Getting Ahead of Security Assessments
You can save time and effort by securely sharing a single security profile, and avoid starting from scratch on every customer security assessment. There aren’t enough hours in the day to respond to each customers’ request!
Improving Communication
If an issue arises regarding a security assessment, you can start direct messaging with your customer without leaving the platform. Thus, cutting down the back and forth and lowering the amount of emails and calls.
To learn more about questionnaire response automation with Beacon by ThirdPartyTrust request your free trial now:
Is responding to security reviews slowing you down?
If your business spends hours each week responding to vendor risk assessment requests, we can help you reduce the time spent answering questionnaires in order to close deals faster.
Learn how to automate the most common questionnaire responses, how to quickly share results of SIG Lite, pen tests, etc., and how to simplify the entire process from NDA to close.