Verizon 2021 Data Breach Report: Is the Cloud Increasing Third Party Risk?
The Verizon 2021 Data Breach Investigations Report was recently released, comprising analysis of 79,635 incidents, of which 5,258 were confirmed data breaches, across 88 countries. In this blog we look at the results through the lens of third party risk and the increased risk surface that came with the switch to the cloud.
Before we dive in, it’s important to understand the terms that the report is based on:
- Incident: A security event that compromises the integrity, confidentiality or availability of an information asset.
- Breach: An incident that results in the confirmed disclosure—not just potential exposure—of data to an unauthorized party.
Verizon 2021 Data Breach Investigations Report Main Findings
The report shows an increase in phishing and ransomware attacks, along with continued high numbers of Web Application Attacks, just as last year’s edition.
The authors pointed out a notable change in how threat actors “will first exfiltrate the data they encrypt so that they can threaten to reveal it publicly if the victim does not pay the ransom”. Ransomware continues to be a threat to all types of organizations, as the latest attack on Colonial Pipeline energy provider showed.
Here are some of the main findings from the Verizon 2021 Data Breach Investigations Report:
- Social engineering is the most successful attack, with Business Email Compromise as the second most common form of social engineering
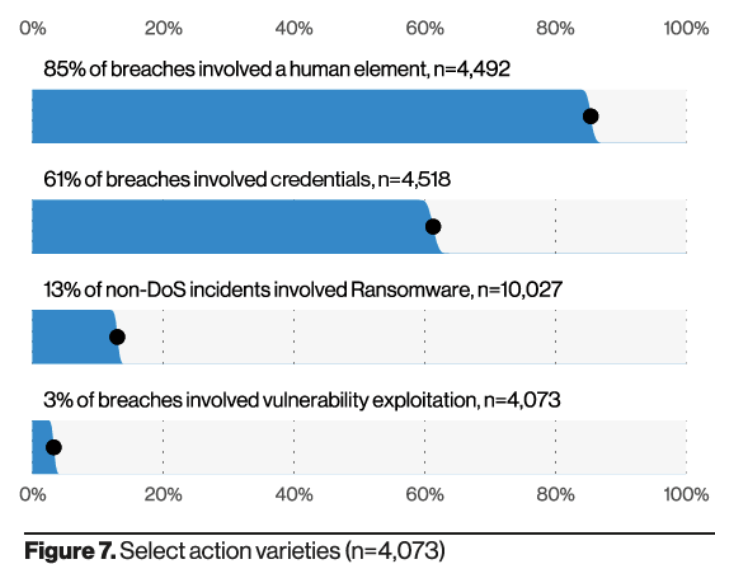
- 85% of breaches involved a human element
- The top cyberattack vector in breaches is web application servers
- Credentials remain one of the most sought-after data types, followed by personal information
- Denial of service is the most frequent way incidents occur
- External cloud assets were compromised more than on-premises assets
- Older vulnerabilities that haven’t been patched are being exploited by attackers
Although some of these findings make the list every year, the context of this edition was unlike any other. 2020 was a year of unprecedented security challenges facing businesses as they moved more of their business functions to the cloud. In fact, attacks on web applications represent 39% of all breaches.
“As the number of companies switching business-critical functions to the cloud increases, the potential threat to their operations may become more pronounced, as malicious actors look to exploit human vulnerabilities and leverage an increased dependency on digital infrastructures”.
Tami Erwin, CEO of Verizon Business
The role of third party vendors and the cloud
In effect, this move to the cloud increased the surface for third party risk and vendor-related data breaches. As more third party vendors join the business ecosystem, organizations need effective and scalable processes to assess their security posture and monitor the relationship lifecycle.
This essentially means:
- Categorizing vendors (including all sorts of suppliers, providers and third parties)
- Defining the requirements each type of vendor will need to fulfill (SOC 2, pentest, PCI compliance, SIG Core, etc,)
- Understanding their inherent risk and impact on the overall health of the network
- Continuously monitoring vendor activity instead of performing point-in-time assessments
Data breaches that occur through a third party vendor are extremely costly and damaging to organizations (here are 5 examples). They don’t always come in the form of sophisticated attacks, but rather phishing or social engineering campaigns that manage to steal credentials.
The problem is, those credentials stolen from one of your vendors could grant attackers access to your business. The report makes it clear that social engineering and basic web application attacks caused the majority of data breaches. Among these, 85% were attributed to a human element. Additionally, 61% involved the use of unauthorized credentials.
Thinking Ahead
It is a common belief that protecting against a vast array of threats demands a complex and revolutionary solution. However, the reality is far more straightforward. Security should be built on strong fundamentals, addressing and mitigating the threats most pertinent to each organization.
Don’t try to boil the ocean if time and resources don’t allow you to build the most comprehensive strategy, but make sure to take steps in the right direction. The infrastructure used in each organization dictates how big its attack surface is.
Start with developing a framework to assess your third party vendors and continue to monitor the relationship according to the level of data handling that’s at stake. Not all vendors require the same controls and assessing their security posture doesn’t have to be a killer if you use automation solutions like ThirdPartyTrust.
For third party vendors responding to security requests, due diligence can also be accelerated and customized so as to avoid repetitive efforts. Check out how ThirdPartyTrust can help scaling the response process.
Recent events around the world have forced a lot of organizations to reevaluate their priorities. We hope these findings and the tips associated with their remediation help you shape your response strategy in the face of an uncertain future.
Interested in vendor risk management? Learn how ThirdPartyTrust can help your organization with risk assessments:




