Web Applications Continue to be a Top Breach Vector for Attackers
Verizon has recently released their 2020 Data Breach Investigations Report (DBIR) and we can see that web applications continue to be a top breach vector for attackers. The report provides valuable insight spanning across 81 countries and 32,002 incidents, of which 3,950 were confirmed data breaches. We looked at the report through the lens of third-party risk and how it relates to perpetuating breaches.
Here are some highlights of the report:
- 43% of breaches involved web applications
- 22% of breached were caused by errors, including misconfigurations and misdelivery of internal information
- 72% of breaches involved large business victims
- 70% were perpetrated by external actors
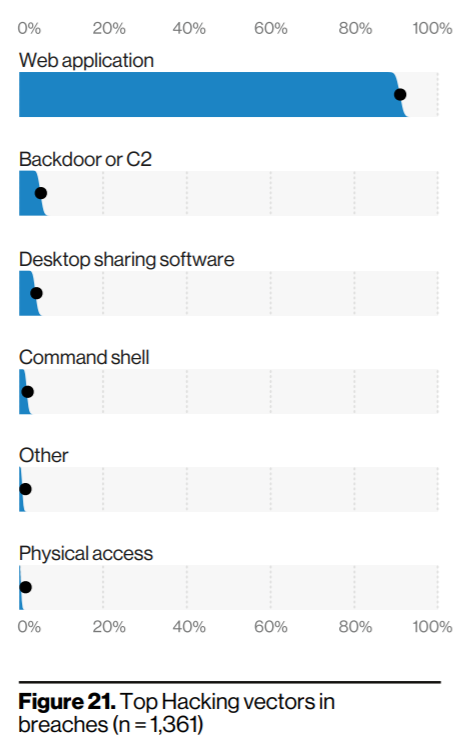
Year after year, web applications continue to be a top breach vector for attackers. Consider the fact that large organizations often outsource some of their tasks to contractors, business associates, and other types of third-parties, who often have access to their network and internal data through web applications.
With the migration of valuable data to the cloud, including email accounts and business-related processes, the risk associated with engaging third-parties has increased. System interfaces delivered as software as a service (SaaS), allowed to move away from manual processes, old spreadsheets and text questionnaires with macros, to streamlined, automated processes conducted through web apps. Also, third-party code is frequently used across all applications, further expanding the attack surface.
According to the report, cloud assets were involved in about 24% of breaches. This includes attacks against the code of the actual web application, such as exploiting code-based vulnerabilities / third-party components, or attacks against authentication, such as use of stolen credentials.
It’s important to note that web application-related breaches rank in the top 2 of nearly all industries analyzed in the report, including: Healthcare, Information, Retail, Financial, Manufacturing, Education, Transportation, Real Estate, and many others.
To name just one example in Healthcare, in June 2019 laboratory testing giant LabCorp disclosed that a breach at a third-party billing collections firm exposed the personal information of 7.7 million North Americans.
It’s clear that cloud security is a big push in the third-party risk management (TPRM) landscape. It has proved to be a cheap, easy to implement solution for nearly all business needs; but it also calls for more controls in place. This not only includes knowing and assessing who administrates the cloud service but also being able to test those controls. Besides thinking about implementing the cloud infrastructure, organizations should think about how it is audited.
Next Steps
Third-party risk audits can definitely make things more manageable. Knowing that stolen credentials are one of the most frequent gateways for attackers, you could check your vendor’s password management policies as part of your due diligence process. This would help bring visibility to potentially bad password management practices which could be exploited to gain credentials for a breach.
There should be constant evaluations, reassessments and upgrades of security infrastructure to meet the current global best standards. This could begin by implementing a secure, purpose-built TPRM workflow management, document repository and process automation platform like ThirdPartyTrust.
It’s not in vain that we say TPRM programs need to get out of email & spreadsheets and move to dedicated tools. If we look at the top threat action varieties in breaches, we can see that misdelivery makes an impressive showing, referring mostly to documents and email that ended up with the wrong recipients.
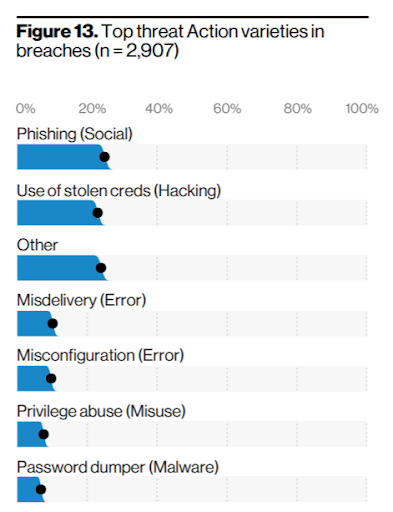
Neither organizations nor vendors can keep sending security documentation (such as insurances, certificates or attestations) via email. It’s insecure, it’s time-consuming, and risky, as the report shows.
To solve this issue, our ThirdPartyTrust platform offers vendors a single profile to easily and securely share their security posture with documents, with encryption in transit and at rest.
Meanwhile, organizations can access those +8,000 vendor security profiles already assessed, and accelerate the third-party assessment/questionnaire review process through automation and centralized communication.
Last but not least, due diligence needs to be complemented with continuous monitoring. These insights can and should be used both for a complete picture of critical third-parties that may have access to sensitive systems and data.
To learn more about how ThirdPartyTrust can help you streamline your TPRM program, request your free trial now:




