007 Life Lessons through the Verizon Breach Report: #2 Communication
We continue with our “007 Life Lessons through the Verizon Breach Report” series, which combines lessons from a gadget wielding international crime-fighter like James Bond with data from the DBIR to secure our enterprises. Today is the turn of lesson 2: Communication.
These lessons come from a recent presentation by our CEO Anders Norremo and Jason Torres from Rush University Medical Center at the 7th Annual Hacking Conference by ISACA and The Institute of Internal Auditors.
Lesson 2: Communication

Fun fact: In Ian Fleming’s books, Q is really the head of the Q division at MI6. Referencing the highest level of security classification.
This name was adopted in modern time by a 4chan poster using the name Q that then morphed into what we hear on the news all the time: Qanon.
Just like James Bond is in constant communication with M and the rest of HQ, so does a well functioning business. But sometimes it’s not so easy.
Communicating Cybersecurity to leadership remains a challenge
Throughout the years, the Verizon Data Breach Investigation Report (DBIR) has shown a common pattern through vulnerabilities and human error. Communication to the affected individuals after a breach remains a topic that is evolving: breaches will eventually happen, so honesty and an ethical approach are always the best choice.
In the Healthcare industry, for example, there are mandatory notification requirements. Also, all 50 states have some sort of communication requirement.
The following table can help shed some light on the importance of cyber security:
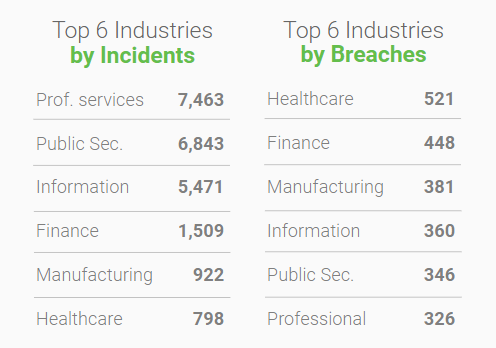
Thanks to this data from the DBIR we know what industries are seeing the most attacks and the most breaches, with Healthcare and Finance at the very top. However, no industry is immune and the companies that are breached are often victims of a crime.
So from a management perspective, it’s fair to ask:
- Are we communicating the message upwards to our Boards?
- Are we communicating the message to our Senior Leaders? What action are they taking?
- Are we communicating the message to our Peers? How are they responding and how are they partnering?
- Are we communicating the message to our internal Cyber teams and other teams? Have they stepped up to help?
Let’s think about what happens when communication goes wrong. If we look at the Uber case, the company got breached and personal information belonging to about 57 million people got exposed. Now its former CSO is facing charges in San Francisco for the attempt to cover-up of the 2016 hack.
The takeaway is breach-related communication (or lack thereof) can impact the organization in so many levels. As stated in the DBIR, the good news is that there is a lot that organizations can do to protect themselves, including the ability to track common patterns within cyber-attack journeys. That way we can take a risk-based approach to areas that need to be addressed.
As always, technology is here to help. Our ThirdPartyTrust platform streamlines communication between enterprises and their vendors to easily track and solve security gaps. When it comes to risk monitoring, our integrated data feeds provide continuous monitoring intelligence for clear and actionable insight to defend against security threats.
To learn more about how ThirdPartyTrust can help you streamline your TPRM program, request your free trial now: