Zero day vulnerability exposed data of 5.4 million Twitter accounts
Twitter has confirmed a zero day vulnerability was exploited to compile a list of 5.4 million user account profiles.
The vulnerability allowed anyone to submit an email address or phone number, verify if it was associated with a Twitter account, and retrieve the associated account ID. The threat actor could then use this ID to scrape the public information for the account, including follower count, screen name, login name, location, and profile picture URL.
Read more: What is a zero day?
In January 2022, the company received a report through their bug bounty program. As a result of the vulnerability, if someone submitted an email address or phone number, Twitter’s systems would tell the person what Twitter account the submitted email addresses or phone number was associated with, if any. This bug resulted from an update to the application code in June 2021.
At first, there was no evidence to suggest the vulnerability had been exploited. But in July 2022, a press report said that someone had potentially leveraged the zero day and was offering to sell the information they had compiled. After reviewing a sample of the available data for sale, Twitter confirmed that a bad actor had taken advantage of the issue before it was addressed.
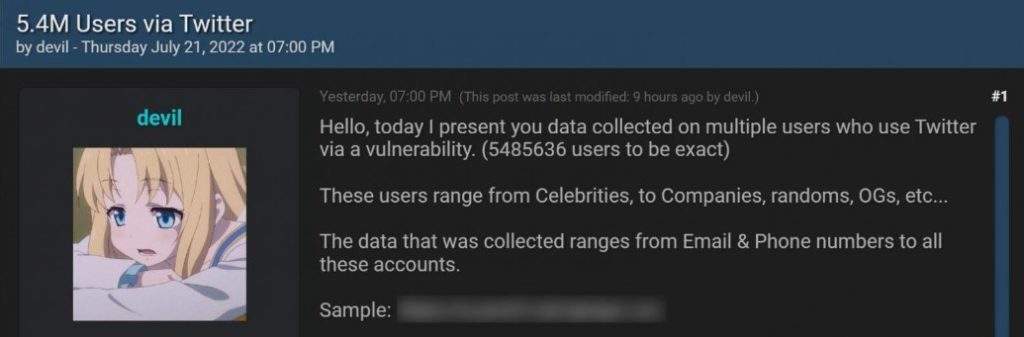
The threat actor was selling the data for $30,000 and told BleepingComputer that there were interested buyers. BleepingComputer later learned that two different threat actors purchased the data for less than the original selling price and that the data would likely be released for free in the future.
This means users should be on the lookout for targeted spear-phishing campaigns utilizing this data to steal Twitter login credentials.
While no passwords were exposed, Twitter is encouraging all users to enable two-factor authentication using authentication apps or hardware security keys to protect their accounts from unauthorized logins.
The rising threat of zero days
A zero day (also referred to as 0-day) is a software vulnerability either unknown to its developer, or known and without a patch to fix it. The name comes from the fact that the vendor has “zero days” to fix before it is actively exploited.
And what is a zero day vulnerability? It’s a software flaw that attackers discover before the vendor does. Because no patch exists yet, attacks exploiting it are likely to succeed.
In 2021, 67% of the most impactful vulnerabilities started with a zero day exploit. And twice as many zero day vulnerabilities were exploited before vendors even had the chance to patch them than in 2020, according to a study by Rapid7.
Read more: Zero day remediation tips
We’ve written extensively about zero day fundamentals in this resource page, including FAQs, practical remediation tips, an on-demand webinar, and an ebook on preventing and remediating zero days.
While headline-grabbing attacks, such as those suffered by SolarWinds, Kaseya, or Log4j have been put under the microscope, many open-source, enterprise applications, and APIs are targets of zero day attacks every day. So how can you be prepared?






