Benefits of integrating TPRM and GRC
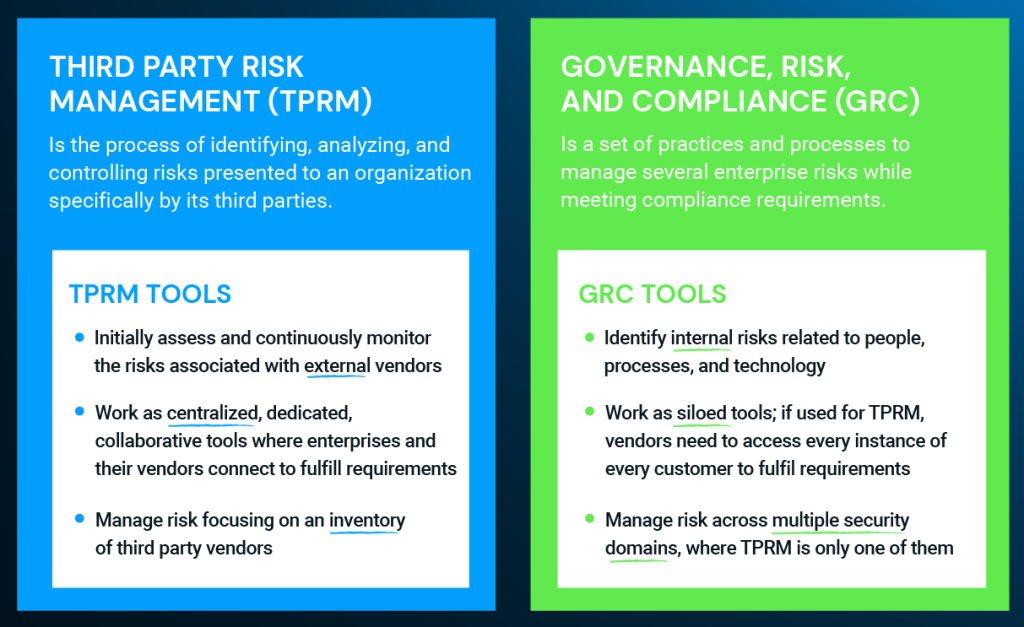
Third Party Risk Management (TPRM) and Governance, risk, and compliance (GRC) are strategic initiatives to reduce enterprise risk. However, risk management and compliance programs are often perceived as siloed, time consuming, manually intensive, check-the-box exercises that create fatigue and prevent effective risk mitigation. So how to make TPRM and GRC work together efficiently?
How is TPRM related to GRC?
GRC is the alignment of people, processes, and technologies with a repeatable framework for risk-based decision making. TPRM is the process of identifying, analyzing, and controlling risks presented to an organization by its third parties, including vendors, suppliers, contractors, customers, or regulators.
While inherently an internal exercise, GRC processes can (and should) be extended to include third party relationships, which are external to an organization. TPRM can be seen as an outward-facing subset of risk, which allows organizations to identify and manage risk across the supply chain to ensure vendors’ adherence to security and compliance requirements.
Specifically, TPRM involves collecting questionnaires and other critical evidence about third party vendors to assess their security posture; understanding what systems or information they have access to and the risk they pose to the organization; ensuring they comply with internal and external regulations; and monitoring any changes in their security procedures over time.
Read More: What is third party risk management? The ultimate guide to TPRM
TPRM and GRC are similar in their approaches and outcomes, with GRC bringing a holistic approach to reduce enterprise risk, and TPRM digging deeper into third and fourth parties in the extended enterprise.
However, when it comes to implementation, TPRM should be treated as a unique risk discipline with a dedicated toolset to optimize vendor risk assessments, vendor onboarding and offboarding, contract management, periodic reassessments, and continuous monitoring.
TPRM tools like ThirdPartyTrust allow organizations to:
- Automate the intake process and the connection with third party vendors to ask them to fulfil requirements
- Build a vendor inventory and categorize them by business impact, department they work with, criticality of service, regulations they need to comply with, etc.
- Customize the assessment requirements based on the type/category of vendor
- Develop processes to focus on the most critical third party vendors
- Understanding and quantifying risk across the vendor population, including risk score, financial viability, privacy policy, data breach history, etc.
- Sending and receiving reminders for vendor security documentation that’s about to expire and needs to be updated
- Monitoring the vendor’s security performance to ensure their services are delivered per the terms of the contract and there are no emerging risk factors
While some organizations use GRC tools (or emails and spreadsheets) to perform these functions, they often result too heavy, non-focused, and siloed to be used for third party risk management purposes.
How modern tools can enhance GRC processes
With data and processes scattered across multiple systems and silos, risk and compliance managers struggle to put the necessary pieces together to make risk-informed decisions aligned with the business strategy.
A successful GRC program needs to change and adapt to reflect an evolving business environment. Organizations can no longer get by with manual, disconnected processes supported by emails and spreadsheets, with differing data and tools across every department.
The biggest strength of GRC tools is to centralize risks across all the different security domains, where TPRM is only one of them. You just need to make sure you have the right toolset to get the TPRM piece of the puzzle.
When you integrate a traditional GRC tool with something more dynamic like a network based TPRM tool, you solve the intake and exchange of information in a much more efficient manner.
Read More: TPRM and GRC: Why you need both tools for your enterprise risk management
Your TPRM platform will provide you with valuable findings on inherent risk and the level of security across your vendor ecosystem. With a seamless integration, you can take all that vendor data into your GRC tool to do a deeper risk monitoring and mitigation.
With a different scope, TPRM and GRC need their own toolset, but work well together to:
- Export vendor risk findings into the overall GRC management
- Gain more visibility and better data to make risk-based decisions
- Increase overall productivity and lower operational costs
Our ThirdPartyTrust TPRM automation platform integrates with your GRC tool:

Requesting and responding to risk assessments should not be a killer
The security assessment process has been slow and time consuming, with manual questionnaires and repetitive requests.
With a Network Approach, enterprises can automate the request of security documentation, and vendors can automate the most common responses to quickly share results of SIG Lite, pen tests, and more.




