Morningstar & Uptake Discuss Vendor Risk Management Best Practices With Anders Norremo
Commercial transactions and informational exchanges no longer represent linear processes between two parties; rather, the shared data travels past the involved entities and into each organizations expansive network of third and fourth party vendors.
Through infiltrating these organizations, hackers are most often able to access the data of larger connected companies. According to a Soha Survey, 63% of all data breaches stem from vendor related attacks. IT experts predict that number of vendor related attacks will rise, as companies increasingly resort to outsourcing for innovation and expanded services.
On July 19th, Anders Norremo, CEO of ThirdPartyTrust, moderated a panel of two experts, Michael Allen, the CIO of Morningstar, and Nick Percoco, the CISO of Uptake, in order to address vendor management concerns as well as other cybersecurity challenges.
Specific topics, asked by Anders, pertained to vendor risk management best practices, overall third-party risk management, the impact of publicized breaches, and how to communicate cybersecurity concerns to executives. Michael Allen and Nicholas Percoco affirmed that an increase in vendor population has coincided with a heightened risk for cyberattacks.

According to Allen, as Morningstar acquired a greater network of vendors, the management process has become more intensive and time consuming.
For Allen, the most time consuming aspects of vendor management includes, conducting time review process, conducting manual review and especially audit reviewing. At Uptake, vendor management also represents a challenge; however, the use of ThirdPartyTrust’s platform has significantly eased the entire process of on-boarding and assessing vendor risk. “We use this really awesome technology, 3PT, which makes things really simple.”
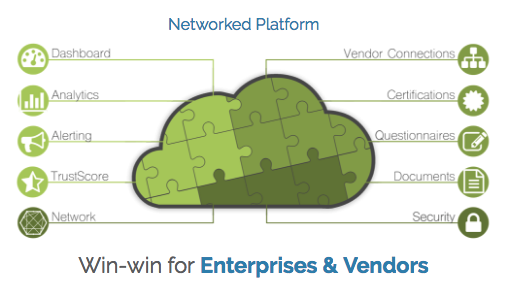
ThirdPartyTrust’s vendor management platform simplifies the collaboration process between the vendor and the enterprise in completing a risk assessment. All necessary data and documentation is consolidated on a single platform, thereby diminishing the hassle of enterprises manually requesting information from their vendors. Furthermore, using a multitude of data points, the platform quantifies the risk and impact of each third and fourth party vendor.
The panelists also discussed best practices for communicating cybersecurity concerns to executive board members.
Percoco does not encounter great difficulty in addressing vendor risk or other security challenges. “Our board members are people in tech who understand the surface level issues”. However, he asserts that this is not always the case. “In my past lives, working in consulting, this was a huge problem”
Michael Allen instructed audience member to tailor their communications style to their audience. “If your audience is the audit and finance guys, speak their language and convert it to the risk they understand.”
The IT experts concluded the conference by stressing the importance of a sound security program, specifically for early stage companies that cannot afford certain security measures, such as SOC Reports and pen tests. Michael Allen described an insufficient security program as a,“liability, that could affect the worth of your company.
Nicholas Percoco further emphasized the importance of having a forward facing story to describe the security controls in place.
“12 Months ago, we were an early stage company that didn’t have a SOC report, but what we did have in place was a story on how we think about security, what measures we have taken, and what our team looks like.”
Want to learn more about ThirdPartyTrust’s Required Documentation feature which streamlines collecting information? Check out the video here.
To learn more about how ThirdPartyTrust can help you manage third-party risk, request your free trial now:




